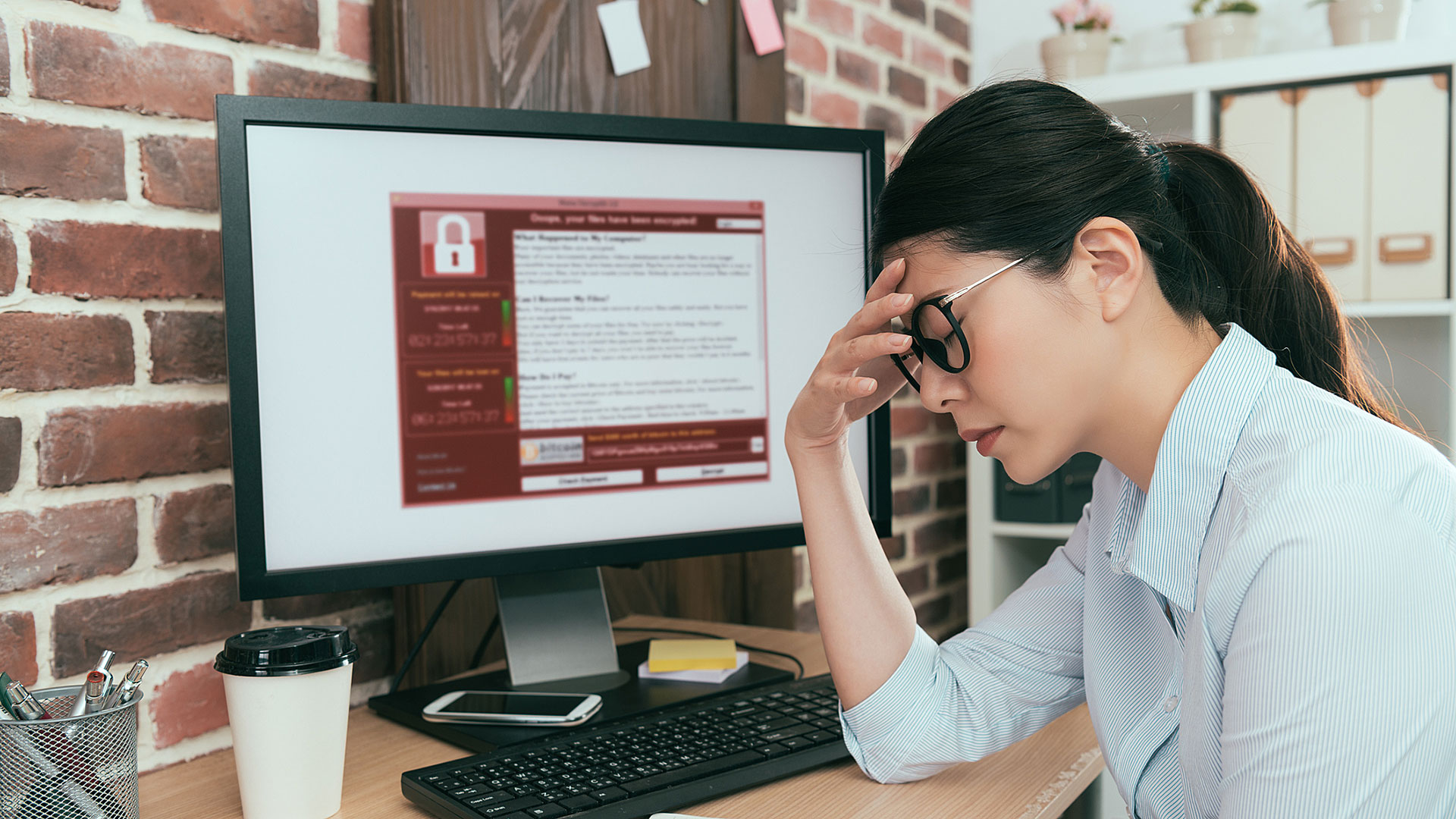
Has Your System Been Corrupted By Ransomware?
Don’t Panic. Here Are Five Steps To Recovery.
You are working on your computer when you notice that things are not running as smoothly as normal; maybe errors begin popping up that a file cannot be opened or a file type is unknown; perhaps you are locked out of your system entirely and when you ping some coworkers, others are experiencing similar issues. Next thing you know, you receive a dreaded message on your screen and your fears are confirmed: your system is being attacked by ransomware.
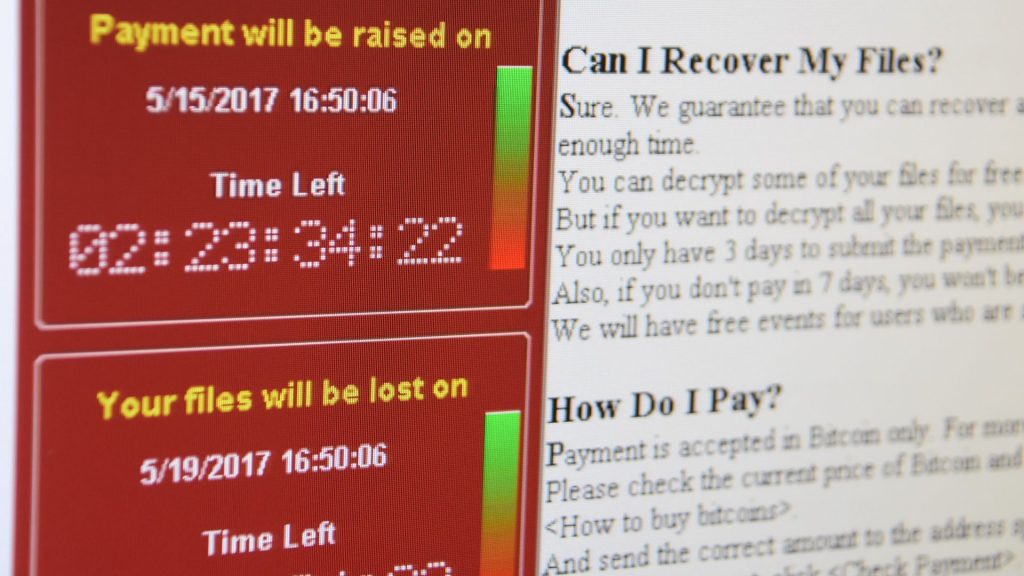
Ransomware is a type of cyberattack where data is locked from users, and oftentimes is encrypted until the company pays a sum to the attacker, often demanded in Bitcoin. These types of cyberattacks are increasing year over year and becoming more dangerous in recent years. These can cost businesses hundreds of thousands or even millions of dollars. In 2020, the average ransom payment increased to nearly $250,000, compared to $100,000 in 2019, an increase of 250%.
As COVID-19 changed the face of how we do business, more and more people work remotely. Cybercriminals are using this to their advantage. Those criminals are hoping that people are working virtually and using computers outside of established networks and more vulnerable to attack. They are also leveraging people’s fear about the pandemic; according to a Bitdefender Threat Landscape report, nearly half of all emails about the novel coronavirus are flagged as spam, one of the key ways malware is delivered to a computer.
How Does Ransomware Work?
Although it can be spread in a number of ways, ransomware is generally delivered via spam, phishing emails, or through social engineering efforts. Infection methods are continuously changing though and there are countless ways one’s technology can come into contact with this malware. Once in place, the ransomware then locks all files it can access by either using strong encryption or restricting access to those files. Finally, the malware demands a ransom to decrypt the files and restore full operations to the infected systems.
Who Should Be Worried?
Everyone. Attackers are agnostic when it comes to sector and business size – no business is too big or too small to be a target. It is also increasingly evident that cybercriminals have no ethical bounds and have attacked schools, hospitals, and government agencies. Older organizations like these often have weaker controls and out-of-date or unsophisticated IT systems and should take extra caution to protect themselves and their data. And although WIndows systems are the most common target, strains of ransomware exist for Macintosh and Linux operating systems as well.
What Do I Do When Attacked?
Firstly, do not panic! Attackers are banking on a user making a quick, poor decisions to help their quest in attacking an organization’s data.
- Record the details of the ransom note, taking a picture with your phone if possible.
- Do not turn off the affected computer but do immediately disconnect it from the network.
- Consider the ransom, remembering that paying does not always guarantee the safety of your data – As an example, the CIty of Baltimore estimates they paid $18.2 million to avoid an approximate $76,000 ransom.
- Consider engaging a firm such as MetroTech that specializes in computer security and ransomware recovery efforts.
- Fix the security problem that allowed for this attack in the first place.
Fixing The Security Problem Has A Number Of Facets.
- Educate your employee population to ensure that phishing attempts and spam are recognized and reported properly.
- Have a data backup plan in place.
- Engage a Managed IT Service Provider that can help you navigate the solutions that will keep your data and business safe.
At MetroTech, we have the experience to help you put the proper technology in place to manage your network and protect your data so that in the event of an unforeseen disaster, that data can be recovered and you can return to normal operations in record time. Call us at (727) 230-0332 today or contact us on our website here. Let’s discuss your current technology and find a solution that is right for you.
